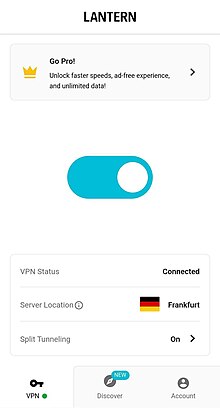
Internet censorship circumvention software
Lantern is a free[a] internet censorship circumvention tool that operates in some of the most extreme censorship environments, such as China, Iran, and Russia.[5] It uses wide variety of protocols and techniques that obfuscate network traffic and/or co-mingle traffic with protocols censors are reluctant to block. It also uses domain fronting.[6] It is not an anonymity tool like Tor.[1]
Lantern was developed and is maintained by Brave New Software Project, a 501c3 nonprofit organization. Brave New Software was founded in 2010 and “is dedicated to keeping the internet open and decentralized through user-focused open tools that solve practical problems in how the internet works for people."
Early versions of Lantern allowed users in countries having free internet access to share their internet connection with those who are in countries where the network is partly blocked.[7] Network connections will be dispersed between multiple computers running Lantern so it will not put undue stress on a single connection or computer.[8]
Lantern's CEO and lead developer is Adam Fisk, is a former lead engineer of LimeWire and LittleShoot.[9]
History
In early versions, Lantern's framework required the use of Google Talk for users to invite other trusted users from their Google Talk contacts.[8] Lantern has won awards from the US Department of State to support internet freedom. This has raised some concerns about the privacy of users, though Fisk has said the State Department is "incredibly hands off" and never dictates how they should write Lantern, or how they should talk about it.[1][8]
In early December 2013, Lantern had a surge of Chinese users and could reach from 200 users to 10,000 users in just two weeks.[10] Soon after that, the network was almost blocked by the Chinese government.[11] Another surge occurred after the 2022 Russian invasion of Ukraine when internet freedoms in Russia were severely curtailed.[12]
The software received US$2.2 million (HK$17.1 million) in seed funding from the US State Department.[13]
Lantern is hosted on a wide variety and continually changing set of data centers around the world. It has used Digital Ocean at times, which was briefly reported as blocked in Iran during the civil unrest on January 2, 2018.[14]
Users are not required to connect by invite since version 2.0 was released in 2015.
Privacy policy
Per Lantern's privacy policy document on their website
Lantern servers do not and will never log:
- Linking Lantern account to real identity (such as purchase information)
- Connection logs (time stamps of connection of IP addresses from client to Lantern server)
- Browsing history
- Traffic destination or metadata
- DNS queries[15]
Lantern collects as little information about their customers as possible in order to run their service:
Our guiding principle toward data collection is to collect only the minimal data required to operate a world-class service at scale. We designed our systems to not have sensitive data about our customers; even when compelled, we cannot provide data that we do not possess.