Variations
Some popular chain codes include:
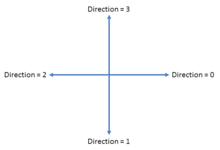
- the Freeman Chain Code of Eight Directions[1] (FCCE)
- Directional Freeman Chain Code of Eight Directions[2] (DFCCE)
- Vertex Chain Code[3] (VCC)
- Three OrThogonal symbol chain code[4] (3OT)
- Unsigned Manhattan Chain Code[5] (UMCC)
- Ant Colonies Chain Code[6] (ACCC)
- Predator-Prey System Chain Code[7][8] (PPSCC)
- Beaver Territories Chain Code[9] (BTCC)
- Biological Reproduction Chain Code[10] (BRCC)
- Agent-Based Modeling Chain Code[11] (ABMCC)
In particular, FCCE, VCC, 3OT and DFCCE can be transformed from one to another[12]
A related blob encoding method is crack code.[13] Algorithms exist to convert between chain code, crack code, and run-length encoding.
A new trend of chain codes involve the utilization of biological behaviors. This started by the work of Mouring et al.[6] who developed an algorithm that takes advantage of the pheromone of ants to track image information. An ant releases a pheromone when they find a piece of food. Other ants use the pheromone to track the food. In their algorithm, an image is transferred into a virtual environment that consists of food and paths according to the distribution of the pixels in the original image. Then, ants are distributed and their job is to move around while releasing pheromone when they encounter food items. This helps other ants identify information, and therefore, encode information.